Privacy for Sale
Your privacy is being attacked yet again as the bill passes to allow the sale of your browsing history.
Check out the Senate roll call list and the House list to see where your representatives stood on the issue.

Your privacy is being attacked yet again as the bill passes to allow the sale of your browsing history.
Check out the Senate roll call list and the House list to see where your representatives stood on the issue.

Another cyberstalking case in Texas, this one has a twist.
“On Monday, a Texas grand jury charged a Maryland man with aggravated assault with a deadly weapon after authorities say he tweeted an animated flashing GIF designed to trigger Newsweek journalist Kurt Eichenwald’s epilepsy last year, immediately causing him to have a seizure.”

U.S. Customs and Border Protection wants to start collecting ‘information associated with your online presence’ from travelers from countries eligible for a visa waiver, including much of Europe and a handful of other countries. Earlier this summer, the agency proposed including a field on certain customs forms for ‘provider/platform’ and ‘social media identifier,’ making headlines in the international press. If approved by the Office of Management and Budget, the change could take effect as soon as December.
Privacy groups in recent weeks have pushed back against the idea, saying it could chill online expression and gives DHS and CBP overbroad authority to determine what kind of online activity constitutes a ‘risk to the United States’ or ‘nefarious activity.'”
As a cyber anthropologist who, at times, uses social media for research – I find this highly disturbing. Twitter is turning into /b where nothing anyone says can really be taken seriously these days. This is ill-conceived and lacks critical understanding of the platform and the culture surrounding it.

Opinion article on Wired concerning the expansion of government surveillance.
“That’s why it’s so concerning that the Justice Department is planning a vast expansion of government hacking. Under a new set of rules, the FBI would have the authority to secretly use malware to hack into thousands or hundreds of thousands of computers that belong to innocent third parties and even crime victims. The unintended consequences could be staggering.”

Fascinating look inside Def Con.
“When I received my press credentials for the convention, they came with a warning that all WiFi networks at the convention and in nearby hotels should be considered “extremely hostile,” which was to be expected at a hacker convention.”
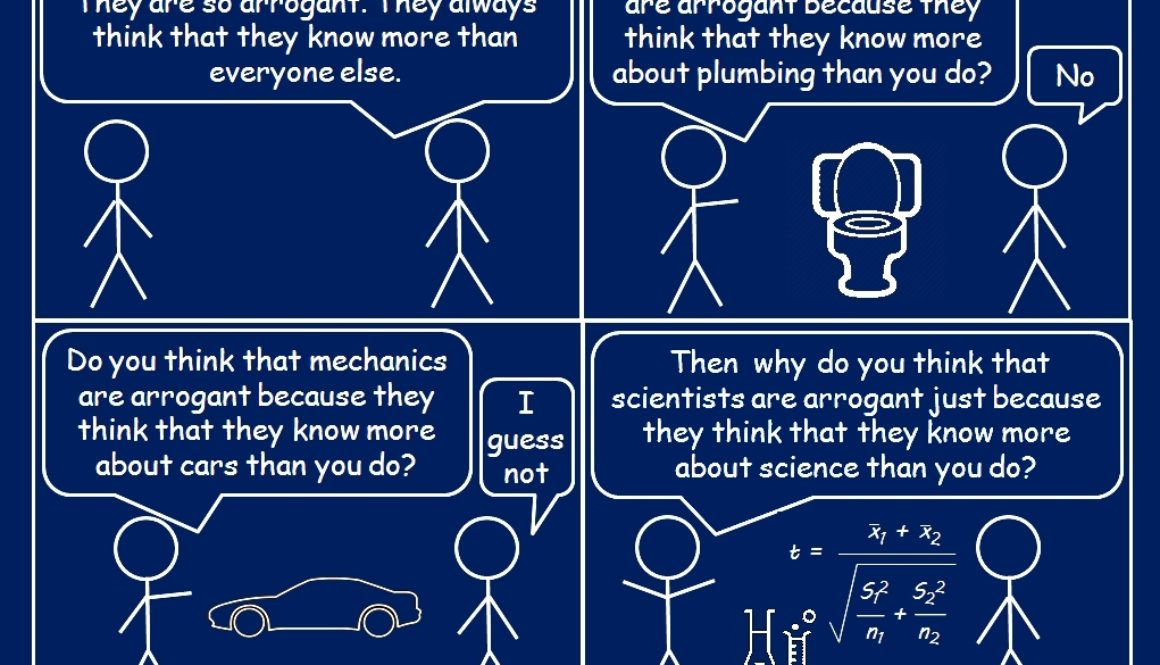
An interesting article on how scientists are so easily dismissed.
“Becoming a professional scientist takes, on average, four years of undergraduate studies (note: science majors are usually rated among the most difficult/time consuming), 6–10 years of intense graduate training (most grad students work/study 60+ hours a week and rarely take holidays), and several years of doing a post-doc. Further, after all of that training, you spend your life actually doing science, which means that you are constantly gaining experience and new knowledge. The idea that reading a bunch of blogs and non-academic books will put you on par with that type of training and experience is the epitome of arrogance and hubris. It is just about the most pretentious thing that I can think of. Of course scientists know more about science than the average person on the street, just as plumbers know more about plumbing than the average person, and mechanics know more about cars than the average person. We intuitively expect that anyone who goes through that type of training will be extremely knowledgeable.”
The following are a list of key findings from my research on parental assessment of video game content appropriateness for their children. You can read the first round of published results here.
Specific answers to research questions will be published in a separate post.
It was mentioned to me that I should update this blog to reflect the fact that I have finally finished my PhD! It only took me 6 years or so, but to be fair I also got married, had twins, and moved to Hawaii in the middle of all of that. So overall, not too shabby of a timeline given those variables.
If you’re looking to get a PhD or in the process of attaining one and you’d like to chat or commiserate, feel free to hit me up on Twitter or in the comments here.
If you’re interested in video games and research in that domain, I’ll be posting results of my study for my dissertation in the days to come!
Here are a few stats from my research on parents and video games copied directly from my dissertation. This post will be the first of several where I talk about my ethnography and the results of my study.
Research Participants
There were 46 total participants in 30 interviews representing 26 households. As defined in Chapter One, a household represents parents who participated alone as well as those who participated together (in the same interview or separately). This singular unit was created to avoid inflation of the numbers where two parents were talking about their shared children and home environments, as that would skew the numbers against those where only one parent participated. Of the participants, 11 were children and 35 were parents. The 35 parents represented 39 qualifying children in total including the 11 who contributed. Of the 35 participating parents, 18 were mothers and 17 were fathers. The parents spanned in ages from 25 to 55. The youngest child participant was 4 and the oldest was 16.
This study afforded opportunities for additional analyses, given the rich qualitative data collected throughout the interviews. Each section below provides this additional information as a way to give context to the research participants and better understand their relationship with video games.
Video Games
Over 200 games were mentioned throughout the course of the interviews, not including the various versions of multiple game franchises. The top three most mentioned games were Minecraft (85% of households), followed by Grand Theft Auto (65%), and then World of Warcraft (42%). Almost two-thirds (64%) of the 39 children played M-rated games and over three-quarters (77%) played T-rated games. None of the children in the study were old enough to purchase M-rated games and only 31% of the 39 children were old enough to purchase T-rated games.
Video Game Devices
Participants played console, computer, and mobile/tablet games equally (88%). Handheld games (58%), followed by web-based (38%), and then educational (35%) rounded out the list. Over three quarters of all 26 households (77%) used some sort of cloud gaming services such as Steam, Origin, Xbox Live, or PlayStation Network. All households downloaded games digitally, whereas only about three-quarters (77%) still bought physical game media.
Video Game Spaces
The majority of game spaces (58%) were publicly shared spaces with the family. Very few (8% of all households) had completely private spaces where stationary devices such as computer towers or consoles were located in children’s rooms. The remaining households (35%) had mixed game spaces due to the use of portable electronics such as laptops, handhelds, and mobile/tablet devices. The majority of households (69%) had some sort of time restrictions placed on video game play; however, less than half of them (39%) considered them to be strict rules.
Parental Assessment
An overwhelming majority of the 26 households (92%) performed some sort of assessment on video games before their children were allowed to play them. Almost all of the 26 households (92%) discussed video game content with their children, and most (85%) stated they knew their children to self-regulate and/or they trusted their children to only play the games of which they knew their parents approved.
Parental Involvement
Almost three-quarters of the 26 households (73%) watched their children play video games and many (69%) played video games with their children. Over half (54%) of the 26 households allowed their children access to the Internet to either play online video games such as massively multiplayer online role playing games (MMORPG i.e., World of Warcraft) which can only be played online, or to play standard multiplayer video games with others online.
You can read about the key findings here. Answers to my specific research questions will be in a different post.
 These are some notes I put together for my team last year. They are based off of a few books I was reading at the time and when I can remember those, I’ll post them for reference. We never made use of these due to reasons other than want and need, but others made find them useful.
These are some notes I put together for my team last year. They are based off of a few books I was reading at the time and when I can remember those, I’ll post them for reference. We never made use of these due to reasons other than want and need, but others made find them useful.
These are just notes. Feel free to fill in any gaps as needed or ask questions if you have any.
Goal:
An experience strategy is a guide for verticals / projects to be referred back to and updated as the vertical and/or project matures. It is a way to maintain focus on the end goal, providing the user with an experience, and is to be shared with and used by everyone on the team. For our purposes, they would likely live in confluences and our bullets would be numbered so we can refer to a specific portion of it when needed. Personas and journey maps as well as other UX artifacts (research before release / usability tests after the fact) would be parts of the experience strategy.
Reasoning:
A strong plan will guide decisions about how the business executes, maintains, and manages experiences to create value for the customers and the business. These should be invested in and managed as well as cultivated and nurtured. A strong experience strategy not only makes it clear what to do, but also what NOT to do.
Start with:
An expression of the experience you hope customers will have. A statement.
Build up:
Bulleted list of experience requirements (not ui / developer requirements, not tasks / goals – it’s all about the EXPERIENCE)
focus on:
user behavior, motivations, context, meaning
usefulness / desirableness
how does it help the user accomplish what they want to get done
how is it (or can be) different / innovative
Big questions:
What do people want to accomplish?
How does this activity fit into their lives?
How can we help deliver on those desires?
Craft:
Hypothesis based on
personas – which are project based, but stem from our basic set
research – which is project based, but builds on all other research – must be actionable and durable
previous testing – which can come from anywhere, but should help craft project based
experience
best practices
analytics
Test:
Against user stories
Against designs
Against prototypes
With Users / Analytics
Iterate and Evolve:
Take all previous information, build on it, then start over if needed.
Strategy should bring clarity and should act as a sign post to show the company where ewe are going and what we need to do to get there.
Consider making it visual when possible.
Leveling Information – so we all start out with the same definitions.
Behaviors:
activities in which people engage
Motivations:
drive and shape behaviors
– understanding the basic drives that lead people to do certain things in certain contexts
Contexts:
help provide meaning to the motivations
learn by doing
Meaning:
worthwhile? important? necessary? required? needed? changes based on context and motivation
Consider:
A user’s experience emerges from:
Motivations
Expectations
Perceptions
Abilities
Flow
Culture
Perception is preceded by sensation and followed by cognition if bottom up, if bottom down – then knowledge influences everything (Gestalt).
Ability – consider memory, it includes sensory (get attention), working and encoding (requires heavy attention), long-term and retention (storage). Recall falls off dramatically after 1 day – this is an issue for users who do not / would not / don’t need to / shouldn’t have to – interact with us or a particular tool / experience on a daily basis. Always something to consider. Reduce memory load / ability requirement whenever possible.
Flow – form follows function. Affordance means there is no need to learn. Avoid multi-usability (modes).
Form hypothesis – test hypothesis whenever possible early and then test again with analytics later. (See my pyramid)
Users / Personas in terms of behaviors, motivations, context and meaning:
Who? – are they
What? – do they need, want, use, are they trying to accomplish and is there a better way to do it
Why? – do they need it, want it, use it, like it, dislike it
Where? – do they need it, want it, use it, expect to find it / access it
How? – do they need it, want it, use it, does it fit into their workflow
Complexity:
Theories should be as simple as possible, but no simpler.
Acknowledge and embrace the complexity
Look for differentiators here – avoid parity, novelty, and trying to “be the best†at everything – just boil it down to the essentials, and then go a step further into the murky and complex chaos of the user until you come out on the other side with something that resonates with the users behaviors and motivations while considering the context and meaning
I think one of the things people fail to realize about the possibility of this Apple backdoor is that it not only has implications for us as Americans, but also for people all over the world.
Consider what doing this would mean for people who live their daily lives in danger when the only protection afforded to them or their loved ones may be the fact that their privacy is secure and their data encrypted.
Consider what it may mean for journalists or whistle blowers.
Many people all over the world only access the Internet through mobile devices. It’s all they can afford. They may even make their living doing so. What if that was taken away because it was no longer considered secure?
Consider everything you have done with your devices knowing they are secure and what may change in your life if at some point it no longer was.
It’s World Anthropology Day. I challenge everyone to look around the world a little differently today to see if they can empathize with people who live in situations completely different from their own. I challenge you to consider what your life would be like if your privacy no longer existed and you had to live in fear – this is reality for so many.
Relevant Links:
https://www.ted.com/talks/jan_chipchase_on_our_mobile_phones?language=en
How Mobile Phones are Changing the Developing World
Pew Report on Communications Technology in Emerging and Developing Nations
 I get a few inquiries each semester from students looking for information on how to get into user experience design, especially those with an anthropology background. I generally try to respond to each of these separately as they each have their own perspective and needs, however, this semester I am trying to get my dissertation defended on top of my every day job as a UXD (which is getting more complicated by the minute). So, rather than leave these unanswered, I am providing a public response here that includes the most common things I share. If you have comments or questions, please leave them! It will be easier for me to respond to those here than individual emails and you may help someone else who has a similar inquiry.
I get a few inquiries each semester from students looking for information on how to get into user experience design, especially those with an anthropology background. I generally try to respond to each of these separately as they each have their own perspective and needs, however, this semester I am trying to get my dissertation defended on top of my every day job as a UXD (which is getting more complicated by the minute). So, rather than leave these unanswered, I am providing a public response here that includes the most common things I share. If you have comments or questions, please leave them! It will be easier for me to respond to those here than individual emails and you may help someone else who has a similar inquiry.
Response Below
Thank you for reaching out to me. Let me start out by saying that having a background in anthropology will lend itself greatly to UX design, however, it is only one part. My suggestion is to consider opportunities where you will be asked to learn to program or script (even just HTML/CSS) and have real users use what you create. This is not necessarily where your career path as a UXD will take you, but creating something, having users use it, and then having to “fix” it to make it better for them, will provide you with insight that no degree program will ever do.
After that, I suggest looking into classes in cognitive psychology and information architecture or information behavior. Adding those to your anthropology perspective will help you find out what users want and then understand what they really need – which may be two separate things. 😉
As for internships, consider looking into the agency world. What I mean by that is marketing/creative agencies that do campaigns for other companies. Not that you want to go into marketing, I prefer the high tech/application world myself, but it allows you to see how UX is applied to multiple groups of people and projects in a short amount of time. A lot of times you can find UXD or IA (information architecture) opportunities – both of which would be beneficial to you.
I also suggest looking into these authors: Steve Krug, Don Norman, Jakob Nielsen, Jesse James Garrett, Luke Wroblewski, Lois Rosenfield, and Peter Morville (These are just off the top of my head, they will give you a good introduction to user experience design – but there are plenty more out there to learn from!)
And I suggest taking a look at the UX Slack channel that has UXers from all over the world lending their perspectives to the field (and it may lead to internship opportunities).
I hope that helps!
End Response
There is a lot that could be added to this, however, I feel it is a great place for people to start. I definitely recommend everyone going into user experience design have some sort of programming or scripting background where people have had to use what you create. My biggest failure as a developer led me to becoming a UXD and in my particular field I use skills I learned as a systems administrator/developer all the time. Not that I do those things anymore, but my past experiences and my understanding of those things definitely help inform me how to make those things easier for others to do. And really, that’s the best part of being an anthropologist and a UXD – being able to use your own experiences to inform your designs. That is, after all, what participant observation is all about!
To learn more about my professional experience, please visit my design and ethnography site.
p.s. This may be edited and updated as I have time. If you have questions/comments – please post them!
So, my last post was in February, and there is a very good reason for that. That was the month I got my IRB approval for my dissertation research and the same month my husband left for a nine-month tour in Korea. So, here I’ve been working full-time, being a full-time mom and working on my dissertation.
The working title for my information science dissertation so far is Understanding Parental Information Behavior in Assessing Video Game Content for their Children: An Ethnographic Study. I’ll be using ethnographic methods similar to the ones I used for my Masters thesis including both in-person and virtual semi-structured interviews with parents, an online survey, and observing parents shopping for video games. You can learn more about it at ResearchingVideoGames.
I’m currently analyzing my interviews and will be seeking approval IRB approval for my survey as the fall semester begins. If you are a parent of a child who plays video games and is between the ages of 4 and 17, feel free to email me at researchingvideogames [@] gmail in order to be notified when the survey becomes available. As a parent, you don’t have to be a gamer to participate.
I shall now return you to your regularly scheduled broadcasts!
While you may have never asked yourself this question, you may have had friends or family that passed on and wondered what happens with their account now as it stands in tribute to their memory.
Facebook has recently released a feature that allows you to bequeath access to certain parts of your Facebook account (pinning a post, updating profile picture and cover photo) to a trusted friend or family member and the access is only granted to them after you have passed. You can access this option under Settings > Security > Legacy Contact.
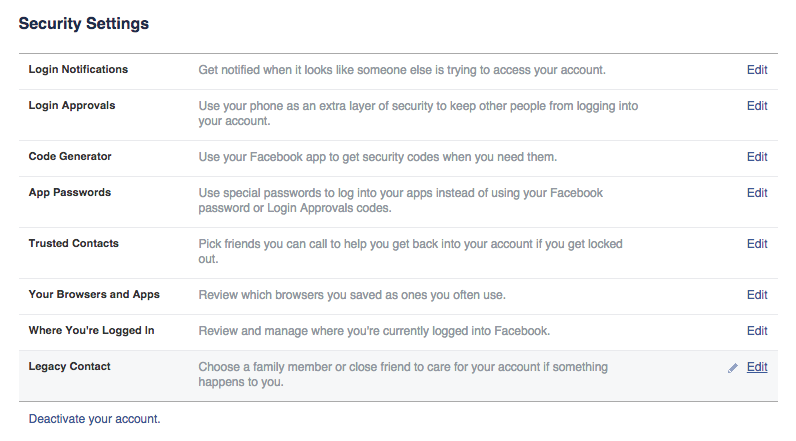
Would you use this? Why or why not? Though it does grant someone else access to your account, it is somewhat limited and you can decide whether or not you want to allow your benefactor the ability to download your Facebook content.
Learn more about this new feature here.
Following on the heels of last weeks post on my UX Pyramid, I thought I’d talk more about the methods one can use to produce the information that would be used to create the deliverables mentioned in it.
I am an anthropologist first and foremost, so being able to use my anthropological methods in user research is important to me. This particular method uses journaling as a means to gain insights into what the user actually does in the system by having the user document what they do when they do it rather than trying to run them through various fabricated scenarios that we as designers might come up with. This allows us to really see the application (this could be software, games, mobile apps etc.) from their perspective rather than trying to force our perspective on them.
As a part of this process, we ask the user to not only document what they are doing, but also to provide screen shots and any other collateral that might be of note (such as information about another site that may do what they want in a better way).
With the information gathered in the journaling portion of the study, we are then able to provide the users with access to new tools or scenarios we are working on that they may be interested in using. This way we get better feedback as these are parts of the system these particular users actually use.
This research then allows for the segmentation of the user base not only by the type of user they are, but also by the way they use the system and the parts of the application they use the most. All of which provides ample information for personas, concepts, process flows, story boards, and wireframes.
Every now and then my work bleeds over into my blog here and this is one of those such occasions.
I was recently tasked with creating a slide deck to help spotlight all of the things that User Experience (UX) Design could do above and beyond wireframes. As a part of that process, I collapsed a previous slide deck I had crafted about 5 years ago into a single infographic. Though it is a stacked pyramid, it should be thought of more of a cycle. The pyramid was built to illustrate how giving a user experience design a solid foundation would help inform the experience throughout the entire design process, which starts well before any boxes and arrows are placed on a screen. Once you get to the top of the pyramid, the analysis of the design should feed back into the discovery process and reinform the strategy for improvements.
This is hardly news for most of us, however, I always enjoy a simple, concise, and useful infographic – so I thought others might as well. Please feel free to share and iterate on this. I always appreciate the feedback.
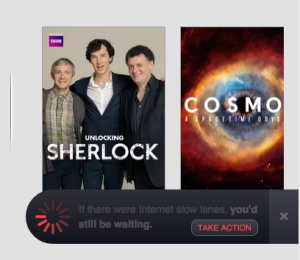
Meaning, if another movie / tv streaming content provider tried to enter the market today without the ability to sign a similar agreement (if only because they were new) they would be unable to even attempt to compete and thus their service would fail before users ever had a chance to try something that may be better or more innovative than the current big kid on the block. While even without net neutrality, enforcing payments like this (rather than the two companies voluntarily entering an agreement) would be legally hard to do today due to current antitrust laws, that doesn’t mean the little guy still wouldn’t find itself in a precarious situation – but perhaps that’s as it should be given the ups and downs of the digital economy.
What is the purpose behind this? Well, the telecom infrastructure in America is largely owned and maintained by private businesses including but not limited to Level 3 Communications, TeliaSonera International Carrier, CenturyLink, Vodafone, Verizon, Sprint, and AT&T. You might recognize the last three as companies from which you purchase your Internet connectivity. It is in their interest to make a profit. But, from what they tell us, it is hard to do that while maintaining and innovating on the infrastructure at the same time.
To my understanding (which could be wrong, I am not a networking expert – feel free to correct me), companies are fighting against the need to use a standard which treats all data the same regardless of what is being carried (i.e. TCP/IP). As an alternative, each company would able to create their own innovations that would help their own networks move data along without that technology necessarily being shared with everyone else. Without chiming in on one side of the debate or the other, this could be very good for consumers in the long run as competition in this area would drive innovation further and further.
The fear is that while competition has somewhat driven the cost to connect down on the consumer side, these companies must find another way to make profits and are looking toward the providers of digital goods as a potential revenue option. To that end, many see these infrastructure companies’ waves against net neutrality as an attempt to charge content providers money to ensure their data reaches their customers as fast as possible. This idea is comparable to a tollway company claiming their roads need maintenance and thus charging stores along the tollway, that have no other way to access them, extra fares to make sure consumers can access the offramps to those stores without delay, while also collecting money from the consumers themselves in order for them to gain access to the tollway in the first place. However, as I said above, this would be difficult to do given the antitrust laws currently in place.
I hope I’ve been able to some what enlighten people as to what the big deal is and I hope I have shed some light on the topic that is not as black and white as most of us have been lead to believe. The lesson to be learned, as with most things on the Internet, is issues such as these aren’t always necessarily as they first appear and a little research goes a long way. This is especially so where government and technology intertwine.
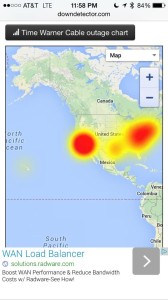
From the spike in reports shown above, it looks like the majority started happening just before midnight HST or 6am EST.
Timing is everything of course. I just cancelled my cable TV today and am now apart of a massive Internet outage. I’m sorry?
There is already speculation as to whether TWC is the latest target of the recent DDOS attacks. I expect more answers will come soon enough, but it’s nearly 1am here in the middle of the Pacific and I have a 8am meeting. Let’s just hope my Internet is up by then as I work from home…
Several gaming news outlets are reporting on the recent gaming outages brought on by a DDOS (distributed denial of service) attack (PCGamer, Joystiq, VentureBeat | GamesBeat) perpetrated by a group calling themselves Lizard Squad. This all came to a head when the SOE (Sony Online Entertainment) President’s plane was diverted due to a bomb threat made by the same group claiming responsibility for the DDOS attacks (Gamespot, Polygon).
I’ll be following this story and making updates on it as it progresses since the FBI is now involved due to the nature of the bomb threat.
Games that were affected by the attack are as follows:
Blizzard.net games including World of Warcraft, Diablo III, Starcraft, Hearthstone
Sony Online Entertainment including Play Station Network
League of Legends
Path of Exile
Were you affected by the outage? Feel free to comment or contact me to let me know about your experience.